Want to Ignore invalid certificate of a device
-
@patrickweiden Hi, sorry for the late reply. I did have a look at the log, unfortunately nothing more enlightening.
The relevant socket connection(s) show:
t=3205 [st=23] SSL_HANDSHAKE_ERROR --> error_lib = 16 --> error_reason = 1040 --> file = "..\\..\\chromium\\third_party\\boringssl\\src\\ssl\\tls_record.cc" --> line = 594 --> net_error = -113 (ERR_SSL_VERSION_OR_CIPHER_MISMATCH) --> ssl_error = 1But I was hoping it would show at least TLS version or what cipher used. I know it does for a working socket connection:
t=1319 [st= 8] SOCKET_BYTES_SENT --> byte_count = 517 t=1457 [st=146] SOCKET_BYTES_RECEIVED --> byte_count = 1360 t=1457 [st=146] SSL_HANDSHAKE_MESSAGE_RECEIVED --> bytes = 02 00 00 55 03 03 4E 30 DE 17 29 56 CC 29 66 78 . U..N0..)V.)fx DA FC 02 78 27 B7 1C 0B 3E 2D 37 4B 63 C0 1A 0B ...x'...>-7Kc... 4A BD 55 A3 EB 9B 20 F1 A4 78 8C 02 4B 52 EE 1F J.U... ..x..KR.. FB 5B A2 61 DB 10 31 92 BD 7B 14 52 28 84 E7 3C .[.a..1..{.R(..< 7C EC 34 4A 34 E5 8E C0 2F 00 00 0D FF 01 00 01 |.4J4.../ ... . 00 00 0B 00 04 03 00 01 02 . .. .. --> type = 2 t=1490 [st=179] -SSL_CONNECT --> cipher_suite = 49199 --> encrypted_client_hello = false --> is_resumed = false --> key_exchange_group = 23 --> next_proto = "unknown" --> peer_signature_algorithm = 1537 --> version = "TLS 1.2"In this case cipher_suite is 49199:
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256In your case a SSL handshake is sent but hardly anything is received:
t=3197 [st=15] SOCKET_BYTES_SENT --> byte_count = 517 t=3205 [st=23] SOCKET_BYTES_RECEIVED --> byte_count = 7 t=3205 [st=23] SSL_ALERT_RECEIVED --> bytes = 02 28So yeah, still no idea why Chromium browsers fail connecting to your device.
Does it listen on plain http and does it work?
@DoctorG said earlier:
"TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 works only if TLS 1.3 is active, tested with Firefox 103 and Chromium 104!"So maybe it tries to use this cipher with an older TLS version (1.0/1.1/1.2?). And maybe Firefox is more forgiving and you've also explicitly set a security exception for this site.
This is why it would be interesting to see
sslscanoutput and alsoopensslconnect output, maybe even trying to do acurlto the device HTTPS interface:
curl -I <device>:<port> -
@Pathduck: You wrote:
You can get the OpenSSL binary from here if you don't have it: https://wiki.openssl.org/index.php/Binaries
This is what my browser currently finds there:
Should we tell the OpenSSL guys about it?

/edit: This morning it works again.

Nevertheless, I managed to organize myself some OpenSSL 3.0.5 binaries to run it...
I ran the
openssl s_client -connect PRINTER-IP:443command and received the following output:
And the
sslscan PRINTER-IP:443led to the following results: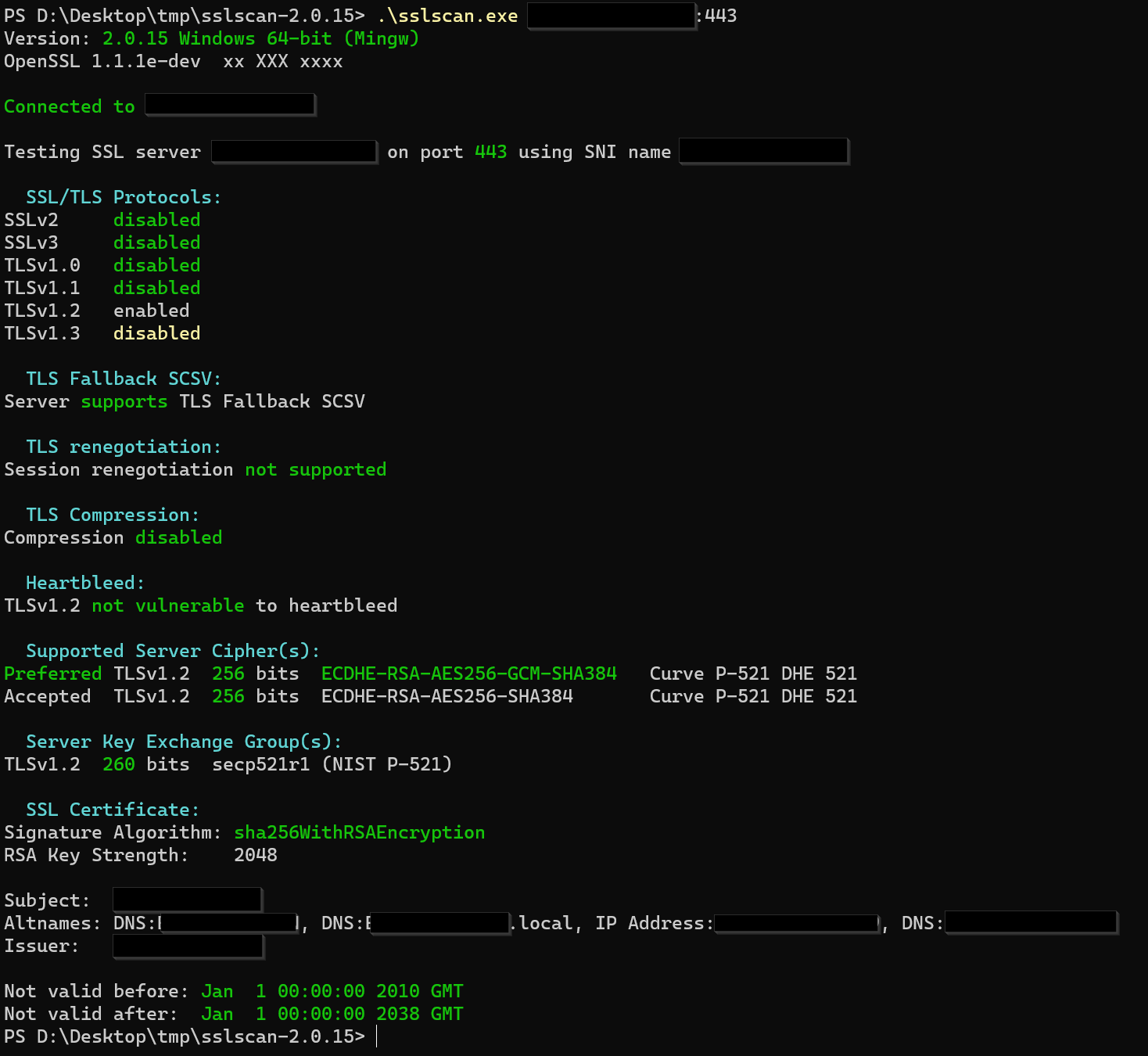
I removed all "irrelevant information" as (DNS) names, IP addresses etc. The certificate is a self-signed certificate from issuer "PRINTERNAME" to subject "PRINTERNAME". If you need further information, please ask for it. Thank you!
/edit:
Does it listen on plain http and does it work?
It has a built-in option to redirect HTTP to HTTPS, which is enabled. I deactivated this redirection and Vivaldi was able to connect to the insecure HTTP variant. The HTTPS variant is still not accessible via Vivaldi (if you explicitly try to reach it via
https://PRINTER-IP).
But at least for the "admin interface" the HTTPS variant should work as you need to enter the admin password (and I do not want to enter it on HTTP variant of the website), so using the HTTP variant is not a real solution here.../edit2:
@DoctorG said earlier:
"TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 works only if TLS 1.3 is active, tested with Firefox 103 and Chromium 104!"
According to this site the mentioned cipher suite also works with TLS 1.2:

So, should not be any issue here as it has been presented by the printer...
-
@patrickweiden Hmm,
seems all ok.
 I do not understand why the printer has only one cipher for TLS 1.2. Weird!
I do not understand why the printer has only one cipher for TLS 1.2. Weird!Connect by IP gives always an error as certificates are only valid for a domain.
-
Heureka!
https://bugs.chromium.org/p/chromium/issues/detail?id=478225
https://bugs.chromium.org/p/chromium/issues/list?q=secp521r1&can=1The secp521r1 is algorithm which is not regarded as secure anymore (weakness was infiltrated by NSA) and removed by Chromium devs.
Can not be enabled by command line or any other internal setting.
-
@Pathduck said in Want to Ignore invalid certificate of a device:
@DoctorG said earlier:
"TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 works only if TLS 1.3 is active, tested with Firefox 103 and Chromium 104!"I could be wrong with test on my crazy web server. Sorry.
-
@patrickweiden can the SSL/TLS on printer administrated to use other ciphers?
Use of only one with the weak cipher suit is really unusual. -
@DoctorG said in Want to Ignore invalid certificate of a device:
@patrickweiden can the SSL/TLS on printer administrated to use other ciphers?
@DoctorG: I was able to change the key size from 256 bits to 192 bits, now "Server Key Exchange Group" section of
sslscansays:TLSv1.2 192 bits secp384r1 (NIST P-384)So, the questionable
secp521r1is no longer in use.Now I can open the website, the only remaining thing is the self-signed certificate. But this I can handle.

Thank you very much for your support!
-
@patrickweiden said in Want to Ignore invalid certificate of a device:
the only remaining thing is the self-signed certificate
Download the public key of the cert and import in your Windows Certificate Store in tree "Trusted Root Certificates"; that helped in the past with self-signed certificates.
-
@DoctorG said in Want to Ignore invalid certificate of a device:
@patrickweiden said in Want to Ignore invalid certificate of a device:
the only remaining thing is the self-signed certificate
Download the public key of the cert and import in your Windows Certificate Store in tree "Trusted Root Certificates"; that helped in the past with self-signed certificates.
Yes, this did help. Entering the subject name of the certificate as
https://CERT-SUBJECTdid yield a valid certificate and now I am even able to store the credentials (which Vivaldi did not offer before due to "invalid certificate").
-
@patrickweiden said in Want to Ignore invalid certificate of a device:
Yes, this did help.
Congrats. Was hard work for you.
-
@DoctorG said in Want to Ignore invalid certificate of a device:
@patrickweiden said in Want to Ignore invalid certificate of a device:
Yes, this did help.
Congrats. Was hard work for you.
Well, yes and no. I just asked and provided information. The remaining things have been done by you.

I find it a little bit annoying that Chromium does not give one the opportunity to choose whether to use a specific cipher, or not. I do not really like the idea that I am not in control of something like this, but that someone else decides things for me...
-
@patrickweiden said in Want to Ignore invalid certificate of a device:
that Chromium does not give one the opportunity to choose whether to use a specific cipher
Command line?
You can block ciphers by a list but not enable single ones.
--args --cipher-suite-blacklist=0x…,0x…
But you need to know the hex value from IANA list for those you do not want to use! -
@DoctorG said in Want to Ignore invalid certificate of a device:
You can block ciphers by a list but not enable single ones.

--args --cipher-suite-blacklist=0x…,0x…Exactly this is the problem. One way is OK (assumed: the way Chromium defines to be "good"), the other not (enabling cipher suites)? Give the user the choice or possibility to do both... (Not what they want?!)
