1.14.1072.3 crash
-
@steffie
Hi, yes it is the same and unfortunately very unstable.Cheers, mib
-
@mib2berlin Oh, i see. Thanks for letting me know. I actually did suspect that it would be like that for you too... once i discovered that even a clean profile, with only the standard V SDs, also crashes, i decided it's something wrong with V-SS not my profile. But i was still unsure, because it seems to me that lots of other users should also be experiencing this, yet nobody else seems to post about it. Puzzling.
-
VB-36600 -- still a problem in 1.14.1077.37 [ie, updating SD TNs still crashes V].
-
@steffie VB-36600 -- still a problem, even in the brand spanking new shiny 1.15.1089.3 [ie, updating SD TNs still crashes V]. This time it took several minutes of SD TN updates [albeit very few TNs actually did update; kinda like V is trying but failing to perform the update task] before the total crash occurred... but it still occurred. Thus, with this bug cursing the past several Snapshots, & now sadly carrying over into the new 1.14 Stable, i no longer have any way to update my SD TNs in V.
-
Hi, just for info, still crash with 1.15.1089.3 every time F5 in subfolder of speed dial.
Opensuse Leap 42.2 x86_64
Intel i5 3570K 16 GB RAM
GTX 760 4 GB /Display card
GTX 670 2 GB
Driver 384.111It work absolut stable with:
Opensuse Leap 42.3 x86_64
CPU Intel T4200 4 GB
GPU Intel GN 965
xf86-video-intel 2.99.917-6.1
KDE Plasma 5.8.7 -
@steffie
Hi, Gwen-Dragon open the thread again for a message.
Today, after update to latest Snapshot 1.15.1090.3 (Official Build) snapshot (64-bit) I reset all changes of vivaldi://flags to default and the crash with F5 is gone.
Cant remember what I changed over time but 10-20 settings for sure.
I will start a list for me to document what I change in flags in the future.Cheers, mib
-
@mib2berlin said in 1.14.1072.3 crash:
I reset all changes of vivaldi://flags to default and the crash with F5 is gone
OMZ, really? That's amazing. Would you pls be kind enough to post back again in another day or two with a further status report? If by then you have continued to have no crashes, then i will have to also reset my flags [but i don't want to do that yet, in case you find that it still crashes anyway]. Thanks.
-
@steffie
Sure, I will do. -
@steffie said in 1.14.1072.3 crash:
VB-36600 -- still a problem, even in the brand spanking new shiny 1.15.1089.3 [ie, updating SD TNs still crashes V].
VB-36600 -- still a problem in 1.15.1094.3 [ie, updating SD TNs still crashes V].
-
@mib2berlin Hi mib, any update yet pls re if your V has continued to NOT crash on SD TN refresh, with your flags reset?
-
Hi, I had not much time to test but not a single crash since I reset flags.
Cheers, mib
-
@mib2berlin Thank you!
FYI, i have now solved it. It's taken hours of tedious testing today, but at least now i know specifically which Flag was causing the crashes. Following my testing, i have been able to re-enable all my desired Flags, with the exception of this culprit:
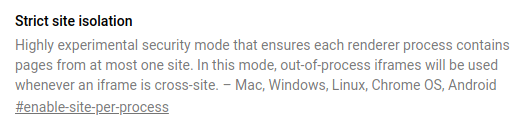
Given i had previously activated that Flag when the bad news about the Meltdown & Spectre flaws become mainstream public knowledge, now discovering that it is incompatible with Vivaldi [SS & Stable] made me nervous to disable it again.
However, thankfully Manjaro Devs have been progressively working their way through various mitigations, & this is my current Tower status [ie, hopefully my disabling this Flag now is offset by these kernel-level patches]:
[steffie@GA-Z97-HD3 ~]$ sudo spectre-meltdown-checker [sudo] password for steffie: Spectre and Meltdown mitigation detection tool v0.34 Checking for vulnerabilities on current system Kernel is Linux 4.15.3-2-MANJARO #1 SMP PREEMPT Mon Feb 12 18:10:47 UTC 2018 x86_64 CPU is Intel(R) Core(TM) i7-4790 CPU @ 3.60GHz Hardware check * Hardware support (CPU microcode) for mitigation techniques * Indirect Branch Restricted Speculation (IBRS) * SPEC_CTRL MSR is available: NO * CPU indicates IBRS capability: NO * Indirect Branch Prediction Barrier (IBPB) * PRED_CMD MSR is available: NO * CPU indicates IBPB capability: NO * Single Thread Indirect Branch Predictors (STIBP) * SPEC_CTRL MSR is available: NO * CPU indicates STIBP capability: NO * Enhanced IBRS (IBRS_ALL) * CPU indicates ARCH_CAPABILITIES MSR availability: NO * ARCH_CAPABILITIES MSR advertises IBRS_ALL capability: NO * CPU explicitly indicates not being vulnerable to Meltdown (RDCL_NO): NO * CPU microcode is known to cause stability problems: NO (model 60 stepping 3 ucode 0x22) * CPU vulnerability to the three speculative execution attacks variants * Vulnerable to Variant 1: YES * Vulnerable to Variant 2: YES * Vulnerable to Variant 3: YES CVE-2017-5753 [bounds check bypass] aka 'Spectre Variant 1' * Mitigated according to the /sys interface: YES (kernel confirms that the mitigation is active) * Kernel has array_index_mask_nospec: YES (1 occurence(s) found of 64 bits array_index_mask_nospec()) > STATUS: NOT VULNERABLE (Mitigation: __user pointer sanitization) CVE-2017-5715 [branch target injection] aka 'Spectre Variant 2' * Mitigated according to the /sys interface: YES (kernel confirms that the mitigation is active) * Mitigation 1 * Kernel is compiled with IBRS/IBPB support: NO * Currently enabled features * IBRS enabled for Kernel space: NO * IBRS enabled for User space: NO * IBPB enabled: NO * Mitigation 2 * Kernel compiled with retpoline option: YES * Kernel compiled with a retpoline-aware compiler: YES (kernel reports full retpoline compilation) * Retpoline enabled: NO > STATUS: NOT VULNERABLE (Mitigation: Full generic retpoline) CVE-2017-5754 [rogue data cache load] aka 'Meltdown' aka 'Variant 3' * Mitigated according to the /sys interface: YES (kernel confirms that the mitigation is active) * Kernel supports Page Table Isolation (PTI): YES * PTI enabled and active: YES * Running as a Xen PV DomU: NO > STATUS: NOT VULNERABLE (Mitigation: PTI) A false sense of security is worse than no security at all, see --disclaimer [steffie@GA-Z97-HD3 ~]$ -
@gwen-dragon Yes, i think you can close that bug report. As we can see, Google prominently warn that this flag is experimental & so i can't really complain that it crashes V ... not V's fault. I'm so pleased to finally know the root cause ... all thanks to @mib2berlin for the idea.
-
 P pafflick unlocked this topic on
P pafflick unlocked this topic on
-
 P pafflick moved this topic from Vivaldi for Linux on
P pafflick moved this topic from Vivaldi for Linux on
