Spying by Vivaldi?
-
I just installed Vivaldi with good hopes for a better private browser, but I see the very first internet accesses by vivaldi.exe are:
239.255.255.250 Unknown (I don't have UPNP on my device)
again 239.255.255.250
and then
31.209.137.18 Another numeric IP (I googled and it is in Iceland!)
then
mimir.vivaldi.comI have updates off. (With on, it was accessing update.vivaldi.com). And home page is /
When closing the browser it goes to another secret numeric IP: 142.250.185.3 (I wonder for what, to call home to state that the user dared to close the browser complete with info?). I checked this IP and it comes out as Google!! So Vivaldi is leaking data to Google?
So is this browser private as claimed, or full of calling home features for the company that made it (and others)?
Does anyone know? -
Welcome to the vivaldi forums!
239.255.255.250 is a multicast adress. It's used for the simple service discovery protocol. Vivaldi is looking for streaming targets (see rightclick -> stream).
The icelandic ip belongs to iceland because vivaldi is an icelandic company, and might (for example) be used to sync the block lists.
That google ip might be anything, I can't tell without testing it for myself. Maybe someone else knows more about it.
For someone naming himself "ITexpert", you're assuming and suspecting way too much with your first post.
Welcome again.
-
@itexpert
Hi, the Google IP is for update extensions and Google services.
You can disable it Settings > Privacy > Google Extensions.
Some user use Googles services like Youtube or Gmail, Vivaldi cant disable all this by default.
Connect to a server does not leak any data automatically.Cheers, mib
-
A great article, possibly a little bit outdated now but explains it well:
https://vivaldi.com/blog/decoding-network-activity-in-vivaldi/The multicast stuff is not talked about, maybe a newer thing. AFAIK hard/impossible to turn off unless going into flags and disabling anything to do with casting. I've tried but gave up, and figured I might find a use for casting one day anyway. It's no biggie, it just spams the local network with requests

Some more doco:
https://en.wikipedia.org/wiki/Simple_Service_Discovery_Protocol -
@mib2berlin
Thank you, I disabled those and the Google on close accesses stopped. -
Spying is such a nefarious word and should belong in the wonderful books of ian fleming.
There is a fundamental difference between telemetry and so called spying.
Vivaldi like many other browsers are based on the chromium codebase and you should expect it to connect to google servers for example to update the safe browsing modules and certificate revocation lists which incidentally are GET requests so nothing is uploaded.
UPNP sounds like a peer networking service although i am hardly an expert myself.
if you install extensions from the google web store then where on earth else would you expect the updates to come from...?.As for the connection to iceland,well seeing as vivaldi has no telemetry,the developers of the browser need an accurate figure of usage and operating systems being installed on..small team really does not need to be wasting it's efforts on an operating system which is hardly used and i would expect windows to be the primary target for development.
my few cents thrown in.
-
@priest72 said in Spying by Vivaldi?:
UPNP sounds like a peer networking service although i am hardly an expert myself.
Universal Plug and Play. So yes, but with autodiscovery features.
-
@priest72
Thank you.
Well, hehe, telemetry is indeed a form of spying, just a nicer word for it.For example, sending "telemetry" of a computer's operating system, hardware spec, programs installed, driver versions, IP address, router spec, etc, are indeed useful to developers! But it is spying, aka sending information of a target system to whoever, Google, Iceland, etc.
Thankfully in the EU we have the GDRP now, where even a plain cookie (3rd party especially) is considers invasion of privacy and requires permission.
It's time for software/apps to require permission as well, before sending completely whatever they want, completely with no control, completely without our knowledge to whoever they chose to! It's Wild West really as things are now. -
Looks pretty innocent to me

https://mimir.vivaldi.com/list/languages.json
24 18:50:13,773638 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 66 6332 → 443 [SYN] Seq=0 Win=64240 Len=0 MSS=1460 WS=256 SACK_PERM=1 45 18:50:13,835563 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 66 443 → 6332 [SYN, ACK] Seq=0 Ack=1 Win=65228 Len=0 MSS=1418 SACK_PERM=1 WS=512 46 18:50:13,835620 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [ACK] Seq=1 Ack=1 Win=262144 Len=0 47 18:50:13,835777 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TLSv1.3 571 Client Hello 48 18:50:13,897407 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 443 → 6332 [ACK] Seq=1 Ack=518 Win=65024 Len=0 51 18:50:13,904364 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TLSv1.3 1472 Server Hello, Change Cipher Spec, Encrypted Extensions 52 18:50:13,904364 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 1472 443 → 6332 [PSH, ACK] Seq=1419 Ack=518 Win=65024 Len=1418 [TCP segment of a reassembled PDU] 53 18:50:13,904364 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 1314 443 → 6332 [PSH, ACK] Seq=2837 Ack=518 Win=65024 Len=1260 [TCP segment of a reassembled PDU] 54 18:50:13,904364 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TLSv1.3 552 Certificate, Certificate Verify, Finished 55 18:50:13,904474 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [ACK] Seq=518 Ack=4595 Win=262144 Len=0 58 18:50:13,932966 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TLSv1.3 134 Change Cipher Spec, Finished 61 18:50:13,934810 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 HTTP 485 GET /list/languages.json HTTP/1.1 84 18:50:13,994784 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 443 → 6332 [ACK] Seq=4595 Ack=598 Win=65024 Len=0 85 18:50:13,995131 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TLSv1.3 357 New Session Ticket 86 18:50:13,995275 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TLSv1.3 357 New Session Ticket 87 18:50:13,995303 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [ACK] Seq=1029 Ack=5201 Win=261632 Len=0 88 18:50:13,996431 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 443 → 6332 [ACK] Seq=5201 Ack=1029 Win=65024 Len=0 89 18:50:13,996872 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 HTTP/JSON 1223 HTTP/1.1 200 OK , JavaScript Object Notation (application/json) 92 18:50:14,038335 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [ACK] Seq=1029 Ack=6370 Win=262144 Len=0 355 18:50:59,017775 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 55 [TCP Keep-Alive] 6332 → 443 [ACK] Seq=1028 Ack=6370 Win=262144 Len=1 358 18:50:59,079144 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 66 [TCP Keep-Alive ACK] 443 → 6332 [ACK] Seq=6370 Ack=1029 Win=65024 Len=0 SLE=1028 SRE=1029 608 18:51:18,997377 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TLSv1.3 78 Alert (Level: Warning, Description: Close Notify) 609 18:51:18,997643 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 443 → 6332 [FIN, ACK] Seq=6394 Ack=1029 Win=65024 Len=0 610 18:51:18,997664 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [ACK] Seq=1029 Ack=6395 Win=262144 Len=0 3572 18:52:04,007639 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 55 [TCP Keep-Alive] 6332 → 443 [ACK] Seq=1028 Ack=6395 Win=262144 Len=1 3573 18:52:04,069354 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 [TCP Keep-Alive ACK] 443 → 6332 [ACK] Seq=6395 Ack=1029 Win=65024 Len=0 3663 18:52:33,597307 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [FIN, ACK] Seq=1029 Ack=6395 Win=262144 Len=0 3664 18:52:33,597328 192.168.0.10 6332 18-137-209-31.business.hringdu.is 443 TCP 54 6332 → 443 [RST, ACK] Seq=1030 Ack=6395 Win=0 Len=0 3703 18:52:33,659135 18-137-209-31.business.hringdu.is 443 192.168.0.10 6332 TCP 60 443 → 6332 [RST] Seq=6395 Win=0 Len=0 -
@ITexpert
Like i said,it is for the benefit of the end user..For example i use linux and i would like to hope linux will still get supported for some time in the future and the outbound connection to iceland every 24hours will ensure this as i am one of many thousands of linux users and i have no problem with it..Just curious as to what you would term a totally private browser as you will find yourself in exactly the same situation with all chromium based browsers and even firefox calls home and has a unique id as does chrome and most of them.
-
That's nice that you use Linux, I would like to use Linux too. What is stopping me is a good firewall.
Do you happen to know of a Firewall for Linux that will ask permission via a pop-up for every internet access of any and all programs running (firewall with "program control"), where you can then allow once/always or block once/always each program? It's my requirement, I wouldn't dream of using a computer as my main where everything can communicate all the time ("telemetry" or otherwise). Stops viruses/scams too.
You could call me naive, but a private browser is a browser that only browses, so will only communicate with the sites the user enters into the address bar. Where all the superfluous stuff can be turned off (e.g. "phishing protection" where the URL the user browses is sent to a big tech company to approve or deny!).
-
@itexpert said in Spying by Vivaldi?:
is sent to a big tech company to approve or deny
That's not how phishing protection works. Nothing is sent to any company. Rather, unsafe site ID lists are downloaded to the client machine and using those lists, the browser blocks access.
-
@itexpert I use puppy linux and have several pups running on 32bit and 64bit and it has zero calling out anywhere,it is a static operating system and the user must update themselves..Used it for a couple of years now and has brought new life to this old computer.
As for a firewall,The only firewall which comes to mind would be the GUFW frontend for iptables which is a graphical interface although i have used the puppy built in firewall mainly.
-
@priest72 said in Spying by Vivaldi?:
Spying is such a nefarious word and should belong in the wonderful books of ian fleming.
Or perhaps to the works of Iam Flaming?
-
@pesala Har har. No, really, har har.
-
Sounds good, but are you sure that is the case for all browsers, including Internet Explorer (that invented it back then) and Edge?
-
@itexpert I am merely chuckling at the pun. I am not referencing browsers, spying or anything. Just the pun. Ian Fleming. Iam Flaming. Hah ha.
-
@itexpert
Thank you all for your quick replies, nice community, I will give Vivaldi a go. -
@itexpert said in Spying by Vivaldi?:
That's nice that you use Linux, I would like to use Linux too. What is stopping me is a good firewall.
Do you happen to know of a Firewall for Linux that will ask permission via a pop-up for every internet access of any and all programs running (firewall with "program control"), where you can then allow once/always or block once/always each program? It's my requirement, I wouldn't dream of using a computer as my main where everything can communicate all the time ("telemetry" or otherwise). Stops viruses/scams too.
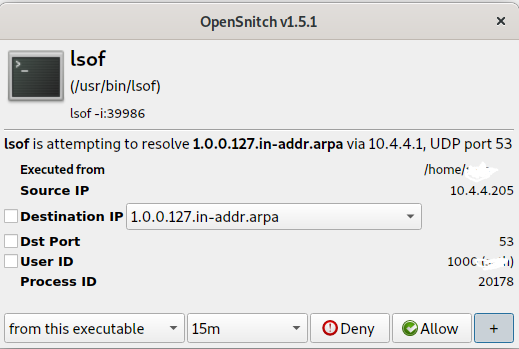
To answer your question first, there is one called OpenSnitch,
but with regard to the first part as well, please don't confuse GNU/Linux, a UNIX-like Operating System, with Microsoft Windows that comes with TONS of unnecessary -well necessary for hackers, malware, M$, their partners and other good boys- proprietary (closed-source) services enabled and running in the background by default, and whose ports you need to block with spending money on software firewalls (analog to the need of buying antiviruses to battle their viruses) as the "press and stores" say, so that you have some sense of control, in most desktop GNU/Linux distributions there are NO running services (who provide ports) in the background by default (with very few exceptions & unless you explicitly open them for your specific program), thus no need for an extra software firewall. You can easily check and admire that in any distro using tools like
ss,lsofandnmap. Additionally in GNU/Linux the network filtering subsystems are in the (open-source) kernel, which is the most scrutinized piece of software in the world.In fact if that reason is the only one stopping you then you are only scratching the surface, because if you do care about privacy and security I must inform you you won't find anything of that in the closed-sourced OS you are using. GNU/Linux has tons of ways further hardening your system, from a hardened kernel, to running proprietary programs isolated (not allowing access to/from the network or the system for example) to using ultra secure distros like Qubes OS.
-
I keep getting this strange Opensnitch popup, everytime I open Vivaldi on loonix. Why would it be running an lsof command every time it launches?